Difference between revisions of "AWS/Connect over SSH to EC2"
(Created page with "= SSH to EC2 instance = ==Theory== SSH theory using a private and public key <gallery widths=400px heights=300px> File:Ssh-pem-pub-keys.png File:Private-public-key.jpg </galle...") |
|||
| Line 55: | Line 55: | ||
*[http://docs.aws.amazon.com/gettingstarted/latest/wah-linux/getting-started-deploy-app-connect.html Connect to Your Amazon EC2 Instance from Windows Using PuTTY] | *[http://docs.aws.amazon.com/gettingstarted/latest/wah-linux/getting-started-deploy-app-connect.html Connect to Your Amazon EC2 Instance from Windows Using PuTTY] | ||
[[Category:ssh]] | [[Category:ssh]][[Category:AWS]] | ||
Revision as of 22:27, 26 May 2014
SSH to EC2 instance
Theory
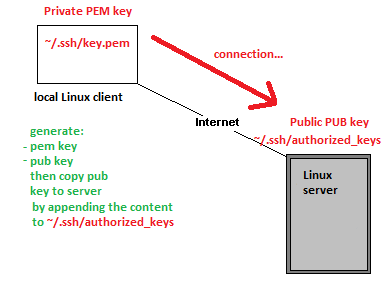
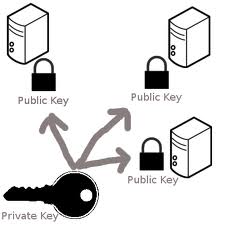
SSH theory using a private and public key
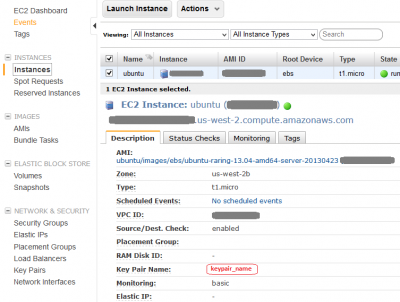
Locate Key Pair on the EC2 Instance screen
Your private key is created when you setup EC2 instance and is listed under EC2 Dashboard > NETWORK & SECURITY > Key Pairs, you must have downloaded a copy of the private key onto your local machine during the instance creation. The key pair used to connect to the specific instance is listed on the Instances screen > Key Pair Name:
Generate private PEM key and public PUB key on Linux client
The command below will generate private/public key pair in the current directory. The file without the extension it is private key, please cat mykey to preview. You will be prompted for passphrase what it adds an extra of security but it can be ignored by pressing [enter] twice.
ssh-keygen -t rsa
Change permissions of the key to ready only by owner as per Getting Started with Amazon EC2 Linux Instances
chmod 400 mykey.pem -r------- 1 user user 1766 Aug 18 01:17 mykey.pem
Copy public PUB key to the EC2 instance
Copy mykey.pub public PUB key to EC2 instance
scp ~/.ssh/mykey.pub ubuntu@ec2-user@ec2-99-99-99-99.compute-1.amazonaws.com:/home/ubuntu/.ssh/
Login to the instance and append mykey.pub to authorized_keys this is know as nstalling the public key to server
ssh ubuntu@ec2-user@ec2-99-99-99-99.compute-1.amazonaws.com cat ~/.ssh/mykey.pub >> ~/.ssh/authorized_keys
Connect to the EC2 instance
- Ubuntu user: ubuntu (confirmed)
- RedHat user: root (tbc)
- Amazon branded instances: ec2-user (confirmed)
From Linux
Connecting and useful flags -l username specifies Linux account user name, -v verbose mode
ssh -i mykey.pem ubuntu@ec2-user@ec2-99-99-99-99.compute-1.amazonaws.com
From Windows
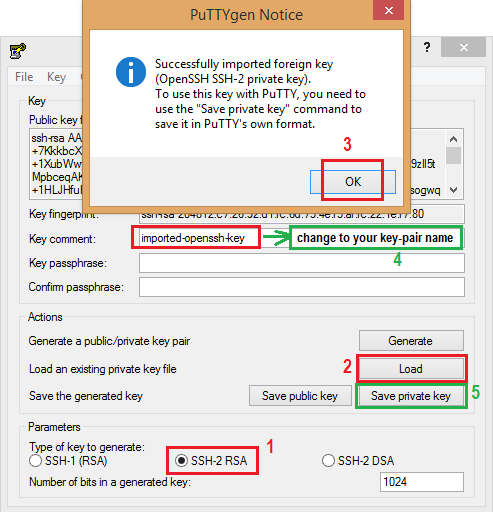
PuTTY does not natively support the private key format (.pem) generated by Amazon EC2. This private key file is in a form called PEM – “Private Enhanced Mail”. PuTTY cannot work with PEM files. PuTTY has a tool named PuTTYgen, which can convert keys to the required PuTTY format (.ppk). You must convert your private key into this format (.ppk) before attempting to connect to your instance using PuTTY.
- To convert your private key
- Start PuTTYgen (All Programs > PuTTY > PuTTYgen).
- Under Type of key to generate, select SSH-2 RSA.
- Click Load. By default, PuTTYgen displays only files with the extension .ppk. To locate your .pem file, select the option to display files of all types(*.*).
- Change Key comment into your instance Key Pair Name made up by you when you created the instance's key pair.
- Click Save private key to save the key in the format that PuTTY can use. PuTTYgen displays a warning about saving the key without a passphrase. Click Yes. Note: A passphrase on a private key is an extra layer of protection, so even if your private key is discovered, it can't be used without the passphrase. The downside to using a passphrase is that it makes automation harder because human intervention is needed to log on to an instance, or copy files to an instance.
- Specify the same name for the key that you used for the key pair (for example, my-key-pair). PuTTY automatically adds the .ppk file extension.
Your private key is now in the correct format for use with PuTTY. You can now connect to your instance using PuTTY's SSH client.
Remove host from SSH known_hosts file
SSH in Linux stores keys for hosts it knows about in ~/.ssh/known_hosts. This is used to detect if a host has changed or compromised. However, recent ssh versions hash the hostname in this file, which is good for security but means you can't just go in and edit the known_hosts file if you want to remove an entry (e.g. the server has been re-built and it now has new keys). The command below will remove the keys for 'hostname' from your known_hosts file. It also works with IP addresses.
ssh-keygen -R hostname
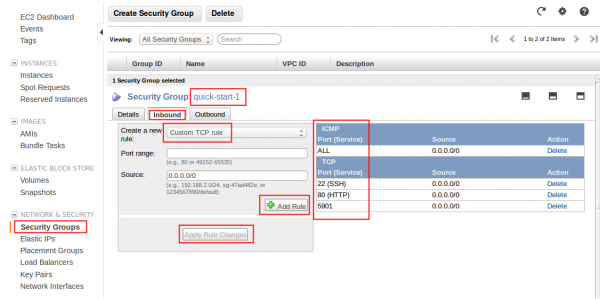
EC2 Security Group
Remember to assign the security group that applies to your scheme on your instance. Having port open on the instance does not mean you will be able to access from outside. It must bypass EC2 Security Group first. Overview below: