AWS/Connect over SSH to EC2
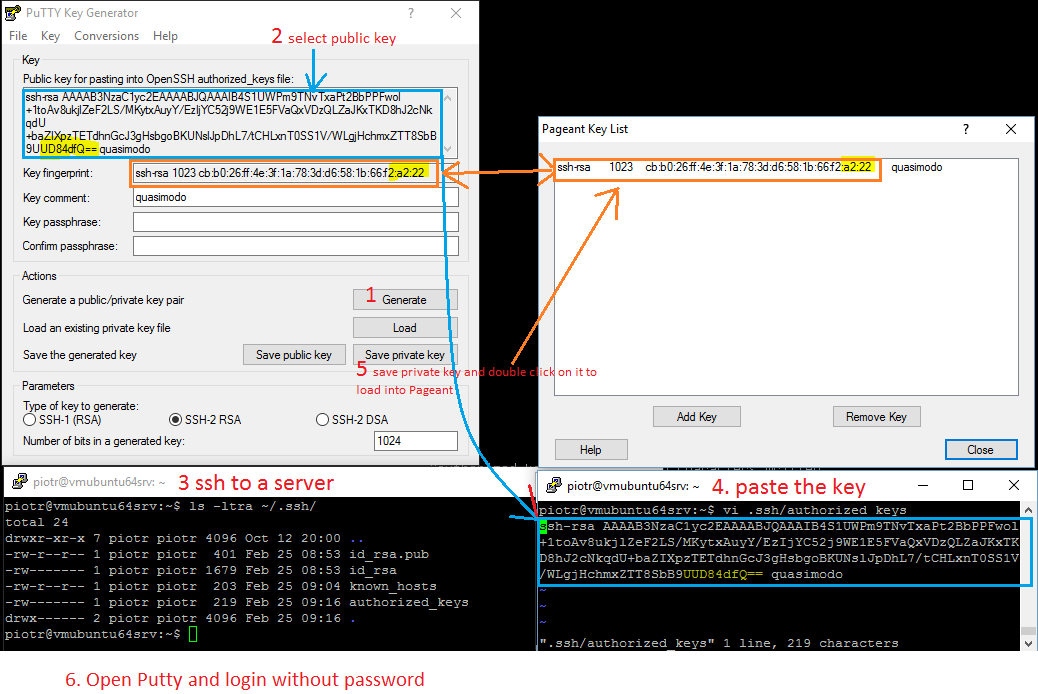
How to connect password-less from Windows Putty to Linux OpenSSH
- Run PuTTYgen.exe and generate a key
- Copy the public key into clipboard. It's already in OpenSSH format
- Login to Linux box and append the key to
~/.ssh/authorized_keysfilevi ~/.ssh/authorized_keys
chmod 600 ~/.ssh/authorized_keys #change permissions if the file did not exist - In PuTTY save the private key on a disk as .ppk file
- Double click on it to load into Pageant (key agent)
- Open Putty and connect to the remote linux box.
The key pair authentication is automatic lookup of matching authorized keys. The key itself does not contain any encoded information like user name or host name, the comment field is arbitrary description not taken into account when connecting.
- The connection will success as long
- the private key is specified in Putty session or loaded into Peagant key agent
- the public key is in
~/.ssh/authorized_keysfile on a remote server where the matching lookup process authenticate the connection
- 6 visual steps to connect
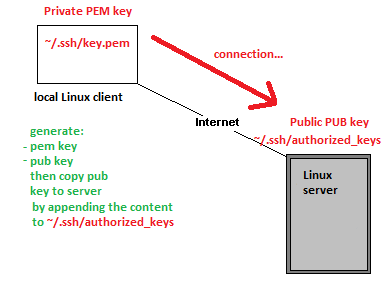
Theory: private and public keys
Ssh protocol can authenticate a user without password by using a private key that is matching a public key installed on a remote server.
- OpenSSH - secure keys management
Each user home has ~/.ssh/ hidden subdirectory with files:
-rw-r--r-- authorized_keys #contains a list of public keys (the contents of id_rsa.pub) one per line that are allowed to
login with the corresponding private key (the id_rsa file)
-r-------- id_rsa #contains the user private key on the current system
-rw-r--r-- id_rsa.pub #contains public key that can be copied/(append to authorized_keys file) on another system
allowing ssh logon without password
-rw-r--r-- known_hosts #contains PUB keys of hosts you connected at least once. If the key is not in you will be prompted:
ECDSA key fingerprint is 0b:4e:13:85:4d:d2:1c:09:b8:6e:4c:20:04:76:c1:bd.
Are you sure you want to continue connecting (yes/no)?
Command ssh-keygen generates interactively a key pair of 2 files in default ~/.ssh location
- id_rsa - private key, stays with us and should never be copied to another system
- id_rsa.pub - public key, to be installed on remote system
You can add PUB keys to known_hosts file by
ssh-keyscan hos1 host2 host3 >> ./.ssh/known_hosts
Theory: ways to connect without password
- You can use a private key id_rsa copied from a remote server to connect to the remote server.
- Or you can append PUB key to authorized_keys file on a remote server and then use the matching private key to connect from a client.
It's worth to note that PuTTY and OpenSSH key files formats are not compatible although both are flat text files.
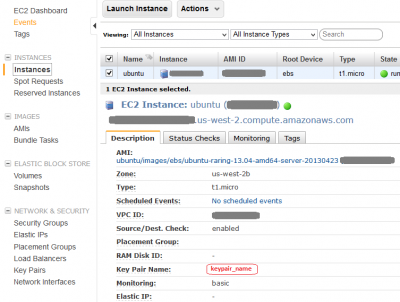
Download private key from EC2 Instance
Your OpenSSH key pair is generated at the time you build EC2 instance. The key pair name used for connection to the instance is listed under EC2 Dashboard > Network & Security > Key Pairs. You should have already downloaded a copy of the private key onto your local machine during the instance creation. The key pair used to connect to the specific instance is listed on the Instances screen > Key Pair Name:
Generate private PEM and public PUB key pair in Linux
The command below generates 2 files that make up a secure key pair, id_rsa file contains a private key and id_rsa.pub file is a public key. During the key generating you will be prompted for passphrase that can add extra layer of security but it can be ignored by pressing [enter] twice. You should also change a file permissions of the private key to read_only by the owner as per Getting Started with Amazon EC2 Linux Instances
ssh-keygen #generates RSA key pair using defaults chmod 400 id_rsa.pem #makes readable only by the owner -r------- 1 user user 1766 Aug 18 01:17 mykey.pem
Password less login - Linux to linux - install public key onto a remote system
For a password less login we need to append public PUB key to a remote system ~/.ssh/authorized_keys file. The public key was generated on our local Linux machine usually has .pub extension. Openssh using ssh-keygen command names creates id_rsa.pub file that contains the public key. The content of this file needs to be added to a remote system ~/.ssh/authorized_keys file. We have two options to achieve this:
- Option 1 - append the key manually
From a local Linux box copy a public key over to the remote host
scp ~/.ssh/mykey.pub ubuntu@ec2-user@ec2-99-99-99-99.compute-1.amazonaws.com:/home/ubuntu/.ssh/
On a remote EC2 instance/linux append content of mykey.pub to ~/.ssh/authorized_keys file. This is known as installing the public key to a server.
ssh {ubuntu|ec2-user}@ec2-99-99-99-99.compute-1.amazonaws.com
cat ~/.ssh/mykey.pub >> ~/.ssh/authorized_keys
- Option 2 - use ssh-copy-id command
This is so called installing identity by pushing our public key from the local machine by ssh-copy-id command that will append .pub key to the remote host ~/.ssh/authorized_keys file. It's important to use FQDN for the remote host
ssh-copy-id -i ~/.ssh/id_rsa.pub {ubuntu|ec2-user}@ec2-99-99-99-99.compute-1.amazonaws.com
Connect to EC2 instance
EC2 default Linux usernames
- Ubuntu user: ubuntu (confirmed)
- RedHat user: root (tbc)
- Amazon branded instances: ec2-user (confirmed)
- CentOS user: centos (tbc)
Connect from Linux
ssh -i myprivkey.pem ubuntu@ec2-user@ec2-99-99-99-99.compute-1.amazonaws.com
-l username #specifies Linux account user name, in example above username ubuntu@ is used
-v #verbose mode
Connecting from Windows using PuTTY
PuTTY does not natively support OpenSSH private key format (.pem) generated on Amazon EC2 instance. This private key file is in a form called PEM – "Private Enhanced Mail". PuTTY cannot work with PEM files. PuTTY has a tool named PuTTYgen, which can convert keys to the required PuTTY format (.ppk). You must convert your private key into PuTTY format (.ppk) before attempting to connect to your instance using PuTTY.
- Convert your PuTTY-gen private key to OpenSSH readable key
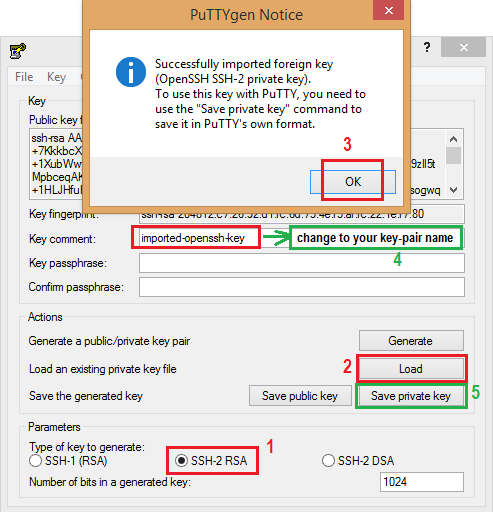
- Start PuTTYgen (All Programs > PuTTY > PuTTYgen).
- Under Type of key to generate, select SSH-2 RSA.
- Click Load. By default, PuTTYgen displays only files with the extension .ppk. To locate your .pem file, select the option to display files of all types(*.*).
- Change Key comment into your instance Key Pair Name made up by you when you created the instance's key pair.
- Click Save private key to save the key in the format that PuTTY can use. PuTTYgen displays a warning about saving the key without a passphrase. Click Yes. Note: A passphrase on a private key is an extra layer of protection, so even if your private key is discovered, it can't be used without the passphrase. The downside to using a passphrase is that it makes automation harder because human intervention is needed to log on to an instance, or copy files to an instance.
- Specify the same name for the key that you used for the key pair (for example, my-key-pair). PuTTY automatically adds the .ppk file extension.
Your private key is now in the correct format for use with PuTTY. You can now connect to your instance using PuTTY's SSH client.
- Connect using a private key
- To do so, you need to specify a path to your private key first.
- Open PuTTY
- Navigate to Connection>SSH>Auth>Private key file for authentication (Browse...)
- Open location of the PPK file to be used for the connection
- Save the session
- Open the session to initiate the connection.
Convert .pem and .ppk private keys
.pem is OpenSSH private key format whereis .ppk is PuTTY prive key format. The puttygen cross platform tool can convert keys.
- Convert in Ubunu
$ sudo apt-get install putty-tools $ puttygen yourKey.ppk -O private-openssh -o yourKey.pem $ puttygen yourKey.pem -O private -o yourKey.ppk
- Convert in Windows
c:\ puttygen yourKey.pem -O private -o yourKey.ppk
-ooutput file-O privateoutput PuTTY private key format-O private-opensshexport OpenSSH private key-O private-sshcomexport ssh.com private key
PuTTY Pageant - pre-load a private key for password less login
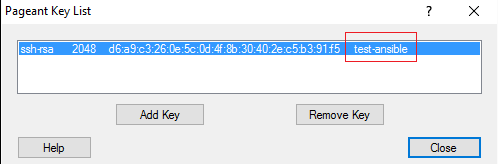
PuTTY Pageant is an agent that holds in a memory a list of private keys (PPK files). When you connect via PuTTY and type in a user name the agent (Pageant) is using matching key to log you in.
- How to use Pageant
Double-click on the PPK file to load into PuTTY Pageant key agent that holds keys in RAM and use them for each connection you do using PuTTY
On successful login in you will see message verifying that you authenticated using a key form an agent (read Pageant)
Remove host from SSH known_hosts file
SSH in Linux stores fingerprints of authorized hosts that can connect to the system in ~/.ssh/known_hosts file. This file is used to detect if a host has changed or may have been compromised. However, recent OpenSSH versions hash the hostname in this file, which is good for security but means you can't just go in and edit the known_hosts file if you want to remove an entry (e.g. the server has been re-built and it now has new fingerprint). The command below will remove an entry for 'a hostname' from your known_hosts file. It also works with IP addresses.
ssh-keygen -R hostname
Generate pub from private key
ssh-keygen -y -f mykey.pem > mykey.pub
Thumbprint aka fingerprint of public key
Sometimes we may have a number private keys and when comparing names it could be confusing. Therefore to uniquely identify the we can use public key thumbprint. Note it's not possible to get private key thumbprint and that would be insecure to share such information. Also useless for a server side. Therefore the snippet below generate public part then generate fingerprint base on it. This also will represent private part of the keypair.
$ file id_rsa #confirm type of file first
id_rsa: PEM RSA private key
for i in $(ls -1 *.pem); do printf "$i "; timeout 10 ssh-keygen -lf /dev/stdin <<< $( ssh-keygen -f ~/.ssh/${i} -y ); done | column -t
This uses the bash here string <<< in order to have stdin available as a regular file /dev/stdin rather than a pipe as ssh-keygen will only operate on a file. As of Release 7.2 of openssh ssh-keygen supports fingerprinting from standard input: ssh-keygen(1): allow fingerprinting from standard input, e.g. "ssh-keygen -lf -".
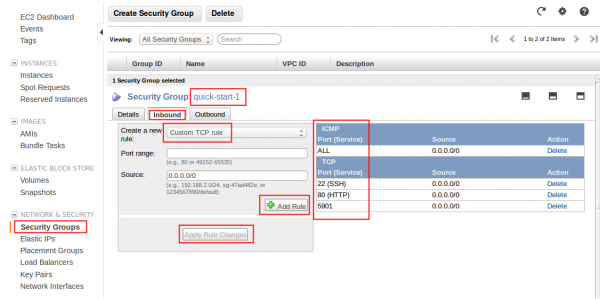
EC2 Security Group
Remember to assign the security group that applies to your scheme on your instance. Having port open on the instance does not mean you will be able to access from outside. It must bypass EC2 Security Group first. Overview below:
Troubleshooting
Error: Could not open a connection to your authentication agent
Ensure ssh-agent is enabled and if not use commands below to run in background:
If you are using Git Bash, turn on ssh-agent:
ssh-agent -s # Agent pid 59566
If you are using another terminal prompt, such as msysgit, turn on ssh-agent:
eval $(ssh-agent -s) # Agent pid 59566
Eval command line break down:
- syntax
$(ssh-agent -s)is equivalent of backticks`ssh-agent -s`and means evaluate and run as a command:
$ ssh-agent -s SSH_AUTH_SOCK=/tmp/ssh-uW2ldhYdWXF4/agent.11701; export SSH_AUTH_SOCK; SSH_AGENT_PID=11702; export SSH_AGENT_PID; echo Agent pid 11702;
ssh-agent -sreturns environment variables soevalcommand tells to shell to run the command output as a script
openSSH - config file
OpenSSH version 7.3 introduced a very handy Include directive.
- Include
- Include the specified configuration file(s). Multiple pathnames may be specified and each pathname may contain glob(3) wildcards and, for user configurations, shell-like ``~ references to user home directories. Files without absolute paths are assumed to be in
~/.sshif included in a user configuration file or/etc/sshif included from the system configuration file. Include directive may appear inside a Match or Host block to perform conditional inclusion.
$ cat > ~/.ssh/config << EOL # Include should be at the top of the file Include ~/.ssh/config.d/linuxAcademy_config Include ~/.ssh/config.d/other/* Host jumpBox HostName 10.0.0.10 User ubuntu IdentityFile ~/.ssh/ubuntu EOL $ cat > ~/.ssh/config.d/linuxAcademy_config << EOL Host la-node-1 HostName 3.33.33.33 User cloud_user IdentityFile ~/.ssh/cloud_user
Mobile secure shell
New generation of ssh try mosh